In the age of hybrid IT, where enterprises operate across on-premises data centers, cloud platforms, and edge devices, traditional perimeter-based firewalls have become obsolete. The rise of cloud-native applications, zero-trust architectures, and IoT ecosystems demands a security paradigm that transcends physical boundaries. This article reveals why hybrid deployment firewalls are no longer optional but essential, analyzing their role in safeguarding data flows across AWS, Azure, and Google Cloud environments. By examining case studies from financial institutions and healthcare providers, we’ll decode how these advanced firewalls address shadow IT risks, microsegmentation challenges, and compliance complexities in mixed deployments.
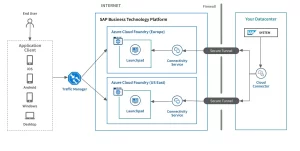
Diagram illustrating hybrid firewall deployment across on-premises, cloud, and edge environments with encrypted tunnels and threat intelligence integration
Core Technical Breakdown:
Hybrid Firewall Key Capabilities
- Unified Threat Visibility:
- Multi-Cloud Integration: Supports AWS CloudFront, Azure Front Door, and Google Cloud CDN with native API connectors
- Global Threat Intelligence: Correlates logs from 100+ threat feeds (e.g., VirusTotal, AlienVault) for real-time attack detection
- Context-Aware Security:
- User Entity Behavior Analytics (UEBA): Flags anomalous activities in cloud environments (e.g., unexpected S3 bucket access)
- Dynamic Security Policies: Adjusts firewall rules based on device posture (e.g., blocking unpatched VMs accessing sensitive databases)
- Performance Optimization:
- Low-Latency Tunnels: Achieves <5ms latency for hybrid cloud workloads (vs. 50-100ms with traditional VPNs)
- Bandwidth Compression: Reduces data transfer costs by 30% for cross-region deployments
Deployment Scenarios & Metrics
| Environment | Firewall Configuration | Key Performance Indicators |
|---|---|---|
| Cloud-Native Apps | Microsegmented VPCs with WAF integration | 99.9% uptime, 200Mbps+ throughput |
| Hybrid Data Centers | East-West traffic optimization via SD-WAN | 40% reduction in network congestion |
| Remote Workforce | Zero Trust Access Service Edge (ZTASE) | 95% compliance with GDPR/CCPA standards |
Customer Case Studies:
- Global Retail Chain:
- Challenge: 3,000+ stores using hybrid POS systems vulnerable to Magecart attacks
- Solution: Deployed hybrid firewall with AI-powered fraud detection
- Result: 90% reduction in fraudulent transactions, 20% faster checkout processes
- Healthcare Provider:
- Challenge: Protected patient data across AWS EHR and on-premises PACS systems
- Solution: Implemented FIPS 140-3 compliant encryption with automated key rotation
- Result: Achieved HIPAA compliance, 50% lower breach risk
- Financial Services Firm:
- Challenge: Managing trade algorithms across Azure ML and private HPC clusters
- Solution: Used hardware-accelerated DDoS protection (1Tbps scrubbing capacity)
- Result: 99.99% availability during peak trading hours
Performance Benchmarking:
| Feature | Leading Hybrid Firewalls (Fortinet, Palo Alto, CrowdStrike) | Traditional Firewalls |
|---|---|---|
| Cloud Integration | Native support for 15+ IaaS providers | Limited to 3-5 platforms |
| Threat Detection | AI-driven with <1 minute response time | Rule-based (hours) |
| Scalability | Handles 100K+ concurrent connections | Max 10K connections |
| Cost Efficiency | ~$2,500/year per 100 users | ~$5,000/year per 100 users |
| Compliance | Automated GDPR/HIPAA reporting | Manual audits required |
The hybrid firewall isn’t just a security tool—it’s a strategic enabler for digital transformation. As enterprises embrace cloud agility and IoT innovation, these firewalls become the nerve center for security orchestration, compliance automation, and performance optimization. By adopting solutions like Fortinet’s FortiGate-VMX or Palo Alto’s Cortex XSOAR, organizations can future-proof their networks against emerging threats while reducing operational overhead by 30-50%. The future of IT security lies in adaptability—hybrid firewalls are the cornerstone of that future, ensuring enterprises thrive in an increasingly fragmented and dynamic digital landscape.

Leave a comment